Still on my way to photography, and a new 50mm thanks to my former colleagues. I shot some more photos that I used as wallpapers in the last months. I offer them to you, CC-BY-SA as usual. Enjoy!

Watch Apple Keynote 2016 on Linux
Linux cannot play Apple Keynote, because Apple uses a so nice technology that the open source OS cannot support? Oh, com’on! Open VLC and select Open Network Stream, then use the following URL: http://p.events-delivery.apple.com.edgesuite.net/1609lijbsdfvoihbadfvohbsdfvljhb/m3u8/hls_mvp.m3u8. For what’s worth… It’s just that I hate being forbidden something for no reason!

Privacy finally reaches the blog
I’m pleased to announce that www.cilyan.org can now be accessed through https, thanks to 1&1 who has added an SSL certificate to its hosting package!
Note: home.cilyan.org still has its own certificate (and will re-open soon).

SWIG and functions with error codes and strerror
SWIG is a wrapper generator that is able to connect compiled libraries to a bunch of scripting languages. The process is mostly automatic, but to tackle some corner cases, you have to help the generator do the right thing. In my library, all functions would return an integer, which is an error code. A special function, following the same behavior as strerror_r, can be used to retrieve the meaning of a special error code. This is a pretty usual mechanism for C code. But that’s not the way scripting languages work. In their world, functions are rather supposed to raise exceptions.
Continue reading
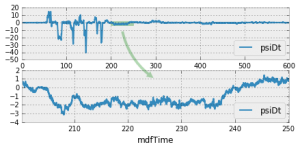
Matplotlib: draw between subplots
Last week, I was preparing a data analysis report using Jupyter, Pandas and Matplotlib (to only quote a few bricks of this wonderful framework). One of the figures had two subplots, the second being an enlargement of a region of the first. To make it obvious, and at the same time show the old MATLAB Fanclub how so 90 they were, I decided to put an arrow from the first to the second subplot.
Alas, from this simple idea started a three hours long research on the Internet, many trials and errors, even a bunch of crashes, and I was close to surrender against the technology of the last century… No way!

Pixabay
A wonderful database of CC0 (public domain) photos and videos to use in all your artworks. Magical!

Bootstrap Arch on Raspberry Pi with only a Wifi dongle
Installing Arch on the Raspberry Pi is rather simple and well documented. There is an offline step, where you copy a base system on the SD card. Then, you place the card in the Raspberry Pi, boot it and you log into that new system somehow, to finish the configuration and start customizing. “Somehow” is either: you plug a keyboard and a screen to the Raspberry Pi and work within the console, or: you plug the Raspberry Pi to your router/computer through an Ethernet cable and log in over SSH. But what if all you have is a Wifi dongle?
Continue reading
Recover root account on Raspberry Pi and alike
“Hey, Pal! How are you? Remember that little project I had on the CubieTruck? I resumed hacking on it. But it’s a pity, I lost my root password… I have to start all over again. Any chance you remember what silly password we choose together?”
If only it was the user’s account password, it would be easy: log as root, change the password on behalf of the user, done. That time, who is going to save the root account? Is there any rootroot account, by any chance? No. But don’t worry, we’re going to hack into the root account nonetheless. But how? It’s Linux, it’s super secure, it’s the root account, I choose a 50-bits-of-entropy-random-super-secure password… Maybe. But almost any security will fail, once the hacker has access to the hardware. And today, we’re the hacker!
Continue reading
Connect the OnePlus X or Two to ArchLinux over MTP
The brand new OnePlus Two and OnePlus X just arrived, and they are beautiful! But as many brand new things, there are some manual tweaks needed to make them cooperate with our beloved system, before the upstream manages to catch up. If the only thing you can access on your brand new OnePlus device is a fake “OnePlus Drivers” CD drive, this post is for you. Don’t worry, it’s dead simple.
Continue reading
Good comments
Good comments don’t tell what, they explain why.